Control theory is an interdisciplinary branch of engineering and mathematics. It deals with the behavior of dynamical systems. The desired output of a system is called the reference. In a control system a controller manipulates the inputs to a system. In the control systems one or more output variables of a system need to follow a certain reference over time.
By manipulating the input, the controller wants to obtain the desired effect on the output of the system. The usual objective of a control theory is to calculate solutions for the proper corrective action from the controller that result in system stability, that is, the system will hold the set point and not oscillate around it.
read more »
Control Theory of Engineering
Cybernetics
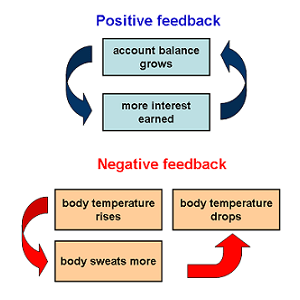
Cybernetics [sahy-ber-net-iks] is the theory of communication and control based on regulatory feedback. This is the original definition of the term; in popular culture the term refers to the study of cyborgs and robotic implants and prosthetics. Cybernetics is only applicable when the system being analyzed is involved in a closed signal loop; that is, where action by the system causes some change in its environment and that change is fed to the system via information (feedback) that enables the system to change its behavior.
A very simple model of cybernetics is that of a central heating system with four elements: a Sensor (to test the system’s environment); a Goal (the specification of the desired state of the system); Error Detection (a method for finding the difference between the present state and the goal state); and an Effector (operations the system can make to get the environment closer to the goal). A more complicated example is the Honda android ASIMO, which uses sensors and sophisticated algorithms to avoid obstacles and navigate stairs.
read more »
Affect Control Theory
In control theory (a theory of sociology that examines controls on societal order), affect control theory proposes that individuals maintain affective meanings through their actions and interpretations of events. The activity of social institutions occurs through maintenance of culturally based affective meanings. Besides a denotative meaning, every concept has an affective meaning, or connotation, that varies along three dimensions: Evaluation (goodness versus badness); Potency (powerfulness versus powerlessness); and Activity (liveliness versus torpidity).
Affective meanings can be measured with semantic differentials yielding a three-number profile indicating how the concept is positioned on evaluation, potency, and activity (EPA). American psychologist Charles E. Osgood demonstrated that an elementary concept conveyed by a word or idiom has a normative affective meaning within a particular culture. A stable affective meaning derived either from personal experience or from cultural inculcation is called a sentiment, or fundamental affective meaning.
read more »
Negative Feedback
Negative feedback occurs when the output of a system acts to oppose changes to the input of a system, acting to stabilize it. The classic example is a central heating system which cuts off when a (suitably placed) temperature sensor hits a pre-set mark. The negative feedback part is the thermostat. Negative feedback is a basic concept of cybernetics (the theory of communication and control based on regulatory feedback in animals and machines).
In biology negative feedback is known as homeostasis (the property of a system, either open or closed, that regulates its internal environment and tends to maintain a stable, constant condition). Virtually all aspects of living systems involve homeostasis (e.g. blood pressure, glucose level, liver functions, cell division). The disruption of feedback loops can lead to undesirable results: in the case of blood glucose levels, if negative feedback fails, the glucose levels in the blood may begin to rise dramatically, thus resulting in diabetes.
read more »
Control Theory of Sociology
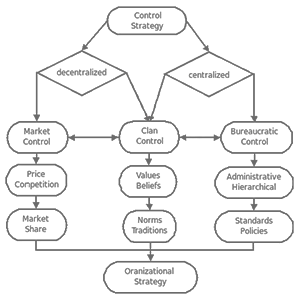
Control Theory is a theory of social order in sociology, which classifies control as centralized or decentralized or neither. Decentralized control is considered market control. Centralized control is considered bureaucratic control. Some types of control such as clan control are considered to be a mixture of both decentralized and centralized control.
Decentralized control or market control is typically maintained through factors such as price, competition, or market share. Centralized control such as bureaucratic control is typically maintained through administrative or hierarchical techniques such as creating standards or policies. Mixed control or clan control is typically maintained by keeping a set of values and beliefs or norms and traditions.
read more »
Meta-reference
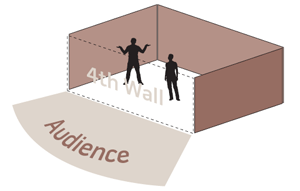
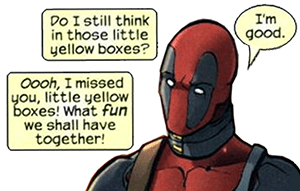
Metareference is a situation in a work of fiction whereby characters display an awareness that they are in such a work. Sometimes it may even just be a form of editing or film-making technique that comments on the show/film/book itself. It is also sometimes known as ‘Breaking the Fourth Wall,’ in reference to the theatrical tradition of playing as if there were no audience, as if a wall existed between them and the actors.
Metareference in fiction is jarring to the reader, but can be comical, as in Jasper Fforde’s novel ‘Lost in a Good Book.’ The character Thursday Next remarks to her husband that she feels uncomfortable having sex in front of so many people, when he is confused because they are alone in their bedroom, she explains, ‘all the people reading us.’ In Fforde’s ‘The Fourth Bear’ two characters lament over a bad joke made by the author, saying, ‘I can’t believe he gets away with that.’ Some novels with first person narration contain instances of metareference when the narrator addresses the reader directly (e.g. Charlotte Brontë’s ‘Jane Eyre’).
read more »
Mise en Abyme
Mise [meez] en [awn] abyme [ah-beem] is a term originally from the French and means ‘placed into abyss.’ The commonplace usage of this phrase is describing the visual experience of standing between two mirrors, seeing an infinite reproduction of one’s image, but it has several other meanings in the realm of the creative arts and literary theory. In Western art history, ‘mise en abyme’ is a formal technique in which an image contains a smaller copy of itself, the sequence appearing to recur infinitely.
In the terminology of heraldry, the ‘abyme’ is the center of a coat of arms. The term ‘mise en abyme’ then meant literally ‘put in the center.’ It described a coat of arms that appears as a smaller shield in the center of a larger one (the Droste effect). For example, the two-headed eagle on modern coat of arms of Russia has a scepter with coat of arms of Russia on top of it, with the same scepter.
read more »
Mirrored Sunglasses
Mirrored sunglasses are sunglasses with a reflective optical coating (called a mirror coating or flash coating) on the outside of the lenses to make them appear like small mirrors. The lenses typically give the wearer’s vision a brown or grey tint. The mirror coating decreases the amount of light passing through the tinted lens by a further 10–60%, making it especially useful for conditions of sand, water, snow, and higher altitudes.
Mirrored sunglasses are one-way mirrors. The color of the mirror coating is independent of the tint of the lenses. It is determined by the thickness and structure of the layer. Their popularity with police officers in the United States has earned them the nickname ‘cop shades.’ Characters in the cyberpunk genre frequently wear mirrorshades, and they are considered a hallmark of the subculture. Many characters in the movie series ‘The Matrix’ exclusively wear mirrored sunglasses, Morpheus in particular.
Hackintosh
OSx86 is a collaborative hacking project to run the Mac OS X computer operating system on non-Apple personal computers with x86 architecture and x86-64 compatible processors. The effort started soon after the 2005 Worldwide Developers Conference announcement that Apple would be transitioning its personal computers from PowerPC to Intel microprocessors. Apple uses a Trusted Platform Module, or TPM, to tie Mac OS to the systems it distributed to developers after announcing its switch to Intel’s chips. A computer built to run this type of Mac OS X is also known as a Hackintosh.
Hackintoshed notebook computers are also referred to as ‘Hackbooks.’ The Apple software license does not allow Mac OS X to be used on a computer that is not ‘Apple-branded.’ The legality of this form of tying is disputed. While the methods Apple uses to prevent Mac OS X from being installed on non-Apple hardware are protected from commercial circumvention in the United States by the DMCA, specific changes to the law regarding the concept of jailbreaking has thrown such and similar circumvention methods when carried out by end-users for personal use into a legal grey area.
Asymmetric Warfare
Asymmetric warfare is war between belligerents whose relative military power differs significantly, or whose strategy or tactics differ significantly. Such struggles often involve strategies and tactics of unconventional warfare (such as subversion and sabotage); the ‘weaker’ combatants use strategy to offset their deficiencies. Such strategies may not necessarily be militarized, involving combatants with widely varying degrees of training and support.
This is in contrast to symmetric warfare, where two powers have similar military forces and resources and rely on tactics that are similar overall, differing only in details and execution. The term is frequently used to describe what is also called ‘guerrilla warfare,’ ‘insurgency,’ and ‘terrorism’ (as well as ‘counterinsurgency’ and ‘counterterrorism’), essentially violent conflict between a formal military and an informal, poorly-equipped, but resilient opponent.
read more »
Union Jack Display
A sixteen-segment display, sometimes called a ‘Union Jack’ display (because it resembles the British Flag), is a type of display based on 16 segments. It is an extension of the more common seven-segment display, adding four diagonal and two vertical segments and splitting the three horizontal segments in half (A fourteen-segment display splits only the middle horizontal segment). A sixteen-segment display can have 65,536 different states; they were were originally designed to display alphanumeric characters (Latin letters and Arabic digits).
Later they were used to display Thai numerals and Persian characters. Before the advent of inexpensive dot-matrix displays, sixteen and fourteen-segment displays were some of the few options available for producing alphanumeric characters on calculators and other embedded systems. However, they are still sometimes used on VCRs, car stereos, microwave ovens, telephone Caller ID displays, and slot machine readouts.
Human Microbiome
The human microbiome is the collection of microorganisms (such as bacteria and fungi) which live on and inside humans (on the skin, in the saliva and mouth, in the eyes, and in the gut and the rest of the gastrointestinal tract). Foreign microbes outnumber human cells in the body a wide margin; humans have about 100 trillion cells, and carry ten times as many microorganisms in the intestines alone.
Some of these organisms are useful for humans. However, most have no known effect; they are just symbionts and are referred to as the normal ‘flora.’ Studies in 2009 asked whether our health is damaged if we reduce this biota (collection of organisms in an ecosystem), which is certainly the case with gut flora (which can be restored by a ‘fecal transplant.’
read more »