Brian Bosworth (b.1965), also known as the “The Boz,” is a former American professional football player. He played college football for the University of Oklahoma, and was a two-time All-American. He played professionally for the NFL’s Seattle Seahawks. In college, he was known for his radical hairstyles and criticism of the NCAA as much as his play on the field. Bosworth was never one to shy from publicity or controversy.
On more than one occasion he referred to the NCAA as the ‘National Communists Against Athletes.’ He wore a shirt bearing that slogan during the 1987 Orange Bowl. Banned from the game because of steroid use, Bosworth unveiled the shirt while standing on the sidelines to the shock and outrage of many, including his own coach, Barry Switzer. While Switzer was known for running a loose ship, this incident was too much even for him, and he threw Bosworth off the team.
read more »
The Boz
Meat Analogue
A meat analogue, also called a meat substitute, mock meat, faux meat, or imitation meat, approximates the aesthetic qualities (primarily texture, flavor, and appearance) and/or chemical characteristics of specific types of meat. Many analogues are soy-based (e.g. tofu, tempeh). Generally, meat analogue is understood to mean a food made from non-meats, sometimes without other animal products such as dairy. The market for meat imitations includes vegetarians, vegans, and people following religious dietary laws, such as Kashrut or Halal. Hindu cuisine features the oldest known use of meat analogues. Meat analogue may also refer to a meat-based and/or less-expensive alternative to a particular meat product, such as surimi (a fish slurry used to make products such as imitation crab meat).
Some vegetarian meat analogues are based on centuries-old recipes for seitan (wheat gluten), rice, mushrooms, legumes, tempeh, or pressed-tofu, with flavoring added to make the finished product taste like chicken, beef, lamb, ham, sausage, seafood, etc. Yuba is another soy-based meat analogue, made by layering the thin skin which forms on top of boiled soy milk. Some more recent meat analogues include textured vegetable protein (TVP), which is a dry bulk commodity derived from soy, soy concentrate, mycoprotein-based Quorn which uses egg white as a binder making them unsuitable for vegans, and modified defatted peanut flour.
Don’t Make Me Think
Don’t Make Me Think is a book by Steve Krug about human-computer interaction and web usability. The book’s premise is that a good software program or web site should let users accomplish their intended tasks as easily and directly as possible. Krug points out that people are good at satisficing, or taking the first available solution to their problem, so design should take advantage of this.
He frequently cites Amazon.com as an example of a well-designed web site that manages to allow high-quality interaction, even though the site gets bigger and more complex every day. The book itself is intended to be an example of concision (brevity) and well-focused writing. The goal, according to the book’s introduction, was to make a text that could be read by an executive on a two-hour flight of an airplane.
Do What I Mean
DWIM (‘Do What I Mean‘) computer systems attempt to anticipate what users intend to do, correcting trivial errors automatically rather than blindly executing users’ explicit but incorrect input. The term was coined by Lisp programmer Warren Teitelman in 1966. Teitelman’s DWIM package ‘correct[ed] errors automatically or with minor user intervention,’ similarly to a spell checker for natural language. Teitelman and his Xerox PARC colleague Larry Masinter later described this philosophy:
‘Although most users think of DWIM as a single identifiable package, it embodies a pervasive philosophy of user interface design: at the user interface level, system facilities should make reasonable interpretations when given unrecognized input. …the style of interface used throughout Interlisp allows the user to omit various parameters and have these default to reasonable values… DWIM is an embodiment of the idea that the user is interacting with an agent who attempts to interpret the user’s request from contextual information. Since we want the user to feel that he is conversing with the system, he should not be stopped and forced to correct himself or give additional information in situations where the correction or information is obvious.’
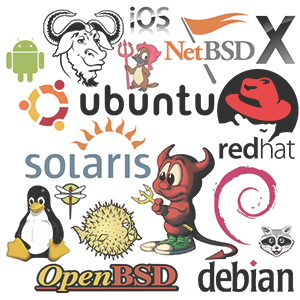
Unix Philosophy
The Unix philosophy [yoo-niks] is a set of cultural norms and philosophical approaches to developing software based on the experience of leading developers of the Unix operating system. Doug McIlroy, the inventor of Unix, summarized the philosophy as follows: ‘Write programs that do one thing and do it well.’ Additional credos include: ‘Write programs to work together. Write programs to handle text streams, because that is a universal interface.’
Richard P. Gabriel, an expert on the Lisp programming language, suggests that a key advantage of Unix was that it embodied a design philosophy he termed ‘worse is better,’ in which simplicity of both the interface and the implementation are more important than any other attributes of the system—including correctness, consistency, and completeness. Gabriel argues that this design style has key evolutionary advantages, though he questions the quality of some results.
Low Orbit Ion Cannon
Low Orbit Ion Cannon (LOIC) is an open source network stress testing and denial-of-service attack application. LOIC was initially developed by Praetox Technologies, but was later released into the public domain, and now is hosted on several open source platforms. It’s named after a fictitious weapon from the ‘Command & Conquer’ series of video games.
The software has inspired the creation of an independent JavaScript version, enabling a DoS from a web browser. LOIC performs a DoS attack (or when used by multiple individuals, a DDoS attack) on a target site by flooding the server with TCP packets or UDP packets with the intention of disrupting the service of a particular host. People have used LOIC to join voluntary botnets. LOIC attacks are easily identified in system logs, and the attack can be tracked down to the individual users IP address.
Topiary
Topiary, real name Jake Davis, is a hacker and self-described ‘Simple prankster turned swank garden hedge. Worked with Anonymous, LulzSec, and other such paragons of intense cyber victory.’ He is an associate of the Internet group Anonymous, which have publicly claimed various online attacks, including hacking HBGary, Westboro Baptist Church, and Gawker. They have also claimed responsibility for the defacing of government websites in countries such as Zimbabwe, Syria, Tunisia, Ireland, and Egypt. 18-year Jake Davis was arrested in Scotland in 2011.
Police confiscated a Dell laptop and a 100-gigabyte hard drive that had 16 different virtual machines. The hard drive also contained details relating to an attack on Sony and hundreds of thousands of email addresses and passwords were found on the computer. A London court released Davis on bail under the conditions that he live under curfew with his mother and have no access to the Internet. His lawyer stated that, while his client did help publicize LulzSec and Anonymous attacks, he lacks the technical skills to have been anything but a sympathizer. After his arrest, Anonymous launched a ‘Free Topiary’ campaign.
The Jester
The Jester (th3j35t3r) is a computer vigilante who describes himself as a grey hat ‘hacktivist.’ He claimed responsibility for attacks on WikiLeaks, 4chan, Iranian President Mahmoud Ahmadinejad, and Islamist websites. He claims to be acting out of American patriotism. The Jester uses a denial-of-service (DoS) tool known as ‘XerXeS,’ that he claims to have developed.
One of The Jester’s habits is to tweet ‘TANGO DOWN’ on Twitter whenever he successfully takes down a website. The Jester had stated that he was a former soldier and had served in Afghanistan and elsewhere.The Jester claims to have originally developed his DoS script as a means to test and harden servers. After learning from an article that Jihadists were using the Internet to recruit and coordinate terror cells, The Jester resolved to disrupting online communications between Jihadists. He weaponized his script and created a front-end known as ‘XerXeS’ in order to solve the script’s usability problems.
read more »
Sabu
Sabu, real name Hector Xavier Monsegur (b. 1983), is an American computer hacker and the founder of the hacking group LulzSec. LulzSec intervened in the affairs of organizations such as News Corporation, Stratfor, British and American law enforcement bodies, and Irish political party Fine Gael.
Sabu later turned informant for the FBI, working with the agency for over ten months to aid them in identifying other hackers from Lulzsec and related groups. His online handle is a reference to a professional wrestler. Monsegur was based out of a housing project on the lower east side of Manhattan while operating as Sabu; he is currently in a witness protection program.
The Intelligent Investor
The Intelligent Investor by Benjamin Graham, first published in 1949, is a widely acclaimed book on value investing, an investment approach Graham began teaching at Columbia Business School in 1928 and subsequently refined with David Dodd. Value investing generally refers to buying securities whose shares appear underpriced. Graham’s favorite allegory is that of Mr. Market, an obliging fellow who turns up every day at the shareholder’s door offering to buy or sell his shares at a different price. Often, the price quoted by Mr. Market seems plausible, but sometimes it is ridiculous.
The investor is free to either agree with his quoted price and trade with him, or ignore him completely. Mr. Market doesn’t mind this, and will be back the following day to quote another price. The point of this anecdote is that the investor should not regard the whims of Mr. Market as a determining factor in the value of the shares the investor owns. He should profit from market folly rather than participate in it. The investor is advised to concentrate on the real life performance of his companies and receiving dividends, rather than be too concerned with Mr. Market’s often irrational behavior.
Utne Reader
Utne Reader [ut-nee] is an American bimonthly magazine, which collects and reprints articles on politics, culture, and the environment from generally alternative media sources, including journals, newsletters, weeklies, zines, music, and DVDs. In addition, the magazine’s writers and editors contribute books, film, and music reviews and original articles which tend to focus on emerging cultural trends. The magazine’s website produces ten blogs covering politics, environment, media, spirituality, science and technology, great writing, and the arts.
The magazine was founded in 1984 by Eric Utne and Nina Rothschild Utne. Utne Reader was part of the salon movement of the 1980s, devoted to debate on the issues of the day, and was an early source of coverage of the mythopoetic men’s movement when it surfaced in the early 1990s. Every year, the magazine gives out its Utne Independent Press Awards, which honor alternative and independent magazines from around the world. Past winners include the ‘Wilson Quarterly,’ ‘In These Times,’ ‘Virginia Quarterly Review,’ and ‘High Country News.’
Obesogen
Obesogens are foreign chemical compounds that disrupt normal lipid metabolism, which can lead to obesity.
Obesogens are functionally defined as chemicals that inappropriately alter lipid homeostasis and fat storage, change metabolic setpoints, disrupt energy balance, or modify the regulation of appetite and satiety to promote fat accumulation and obesity. The term obesogen was coined by Bruce Blumberg of UC, Irvine. The topic of this proposed class of chemical compounds and how to counteract their effects is explored at length in the book ‘The New American Diet.’