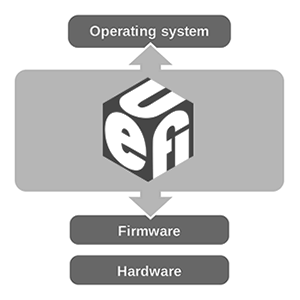
The Unified Extensible Firmware Interface (UEFI) is a specification that defines a software interface between an operating system and platform firmware. UEFI is meant as a replacement for the Basic Input/Output System (BIOS) firmware interface, present in all IBM PC-compatible personal computers. In practice, most UEFI images have legacy support for BIOS services.
It can be used to allow remote diagnostics and repair of computers, even without another operating system. The original EFI (Extensible Firmware Interface) specification was developed by Intel. Some of its practices and data formats mirror ones from Windows. The BIOS is limited to a 16-bit processor mode and 1 MB of addressable space due to the design being based on the IBM 5150 which used the 16-bit Intel 8088. In comparison, the UEFI processor mode can be either 32-bit (x86-32, ARM) or 64-bit (x86-64 and Itanium).
In addition to the standard PC disk partition scheme, which uses a master boot record (MBR), EFI works with a new partitioning scheme: GUID Partition Table (GPT). GPT is free from many of the limitations of MBR. In particular, the MBR limits on the number and size of disk partitions (up to 4 primary partitions per disk, up to 2 TiB per disk) are relaxed. GPT allows for a maximum disk and partition size of 8 ZiB. The UEFI specification explicitly requires support for FAT32 for system partitions, and FAT12/FAT16 for removable media; specific implementations may support other file systems. Note that it does not remove the requirement for target operating system to natively support current partitioning schemes (GPT or msdos MBR) in order to be able to boot and function.
Numerous digital rights activitists have protested against UEFI. Ronald G. Minnich, a co-author of ‘coreboot’ (a freeware BIOS alternative), and Cory Doctorow, a digital rights activist, have criticized EFI as an attempt to remove the ability of the user to truly control the computer. It does not solve any of the BIOS’s long-standing problems of requiring two different drivers—one for the firmware and one for the operating system—for most hardware.
In 2011, Microsoft was accused by critics and open source advocates (including the Free Software Foundation) of trying to use the ‘secure boot’ functionality of UEFI to hinder or outright prevent the installation of alternative operating systems such as Linux, by requiring that new computers certified to run its Windows 8 operating system ship with secure boot enabled using a Microsoft private key. Following the criticism, Microsoft denied that the secure boot requirement was intended to serve as a form of lock-in, and clarified its requirements by stating that systems certified for Windows 8 must allow secure boot to enter custom mode or be disabled, but not on systems using the ARM architecture.
Several major Linux distributions have developed workarounds for secure boot; Ubuntu will use the more liberally-licensed efilinux bootloader (signed with a key compatible with Microsoft’s platform key) as a shim to load GRUB on UEFI systems, which will be used to boot an unsigned kernel. Ubuntu developers believe this practice of only signing the bootloader is more feasible since a trusted kernel would only be effective at securing user space and not the pre-boot state (which secure boot is designed to protect), and that this would also allow users to build their own kernels and use custom kernel modules as well without needing to re-configure the system.
The Daily Omnivore
Everything is Interesting

Leave a comment