Fair use is a limitation and exception to the exclusive right granted by copyright law to the author of a creative work. Examples of fair use include commentary, search engines, criticism, news reporting, research, teaching, library archiving, and scholarship.
It provides for the legal, unlicensed citation or incorporation of copyrighted material in another author’s work under a four-factor balancing test (Purpose and character; Nature of the copied work; Amount and substantiality; and Effect upon work’s value). Along with Public Domain, Fair use is one of the ‘Traditional Safety Valves’ (techniques that balance the public’s interest in open access with the property interest of copyright owners)
read more »
Fair Use
Reverse Graffiti
Reverse graffiti, also known as clean tagging or grime writing, is often done by removing dirt/dust with the fingertip(s) from windows or other dirty surfaces, such as writing ‘wash me’ on a dirty vehicle. Others, such as English artist Paul Curtis (aka Moose), use a cloth or a high power washer to remove dirt on a larger scale.
The first large scale reverse graffiti art piece was made by Alexandre Orion in 2006, the intervention ‘Ossario’ with over 1000 foot is washed by the municipality of São Paulo in the end of the video.
read more »
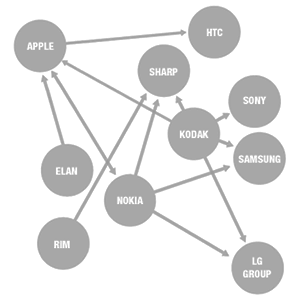
Patent Thicket
A patent thicket is ‘a dense web of overlapping intellectual property rights that a company must hack its way through in order to actually commercialize new technology,’ or, in other words, ‘an overlapping set of patent rights’ which require innovators to reach licensing deals for multiple patents from multiple sources.’ The expression may come from the ‘SCM Corp. v. Xerox Corp’ patent litigation case in the 1970s, wherein SCM’s central charge had been that Xerox constructed a ‘patent thicket’ to prevent competition. Patent thickets are used to defend against competitors designing around a single patent.
It has been suggested by some that this is particularly true in fields such as software or pharmaceuticals, but Sir Robin Jacob has pointed out that ‘every patentee of a major invention is likely to come up with improvements and alleged improvements to his invention’ and that ‘it is in the nature of the patent system itself that [patent thickets] should happen and it has always happened.’ Patent thickets are also sometimes called ‘patent floods,’ or ‘patent clusters.’
Submarine Patent
A submarine patent is a patent whose issuance and publication are intentionally delayed by the applicant for a long time, such as several years. This strategy requires a patent system where, first, patent applications are not published, and, second, patent term is measured from grant date, not from priority/filing date. In the United States, patent applications filed before November 2000 were not published and remained secret until they were granted. Analogous to a submarine, therefore, submarine patents could stay ‘under water’ for long periods until they ’emerged’ and surprised the relevant market. Persons or companies making use of submarine patents are sometimes referred to as patent pirates.
Submarine patent practice was possible previously under the United States patent law, but is no longer practical since the U.S. signed the TRIPS agreement of the WTO: since 1995, patent terms (20 years in the U.S.) are measured from the original filing or priority date, and not the date of issuance. A few potential submarine patents may result from pre-1995 filings that have yet to be granted and may remain unpublished until issuance. Submarine patents are considered by some, including the US Federal Courts, as a procedural laches (a delay in enforcing one’s rights, which may cause the rights to be lost).
Antisec
The Anti Security Movement (also written as antisec and anti-sec) is a movement opposed to the computer security industry. Antisec is against full disclosure of information relating to but not limited to: software vulnerabilities, exploits, exploitation techniques, hacking tools, attacking public outlets, and distribution points of that information. The general thought behind this is that the computer security industry uses full disclosure to profit and develop scare-tactics to convince people into buying their firewalls, anti-virus software, and auditing services. As recently as 2009, attacks against security communities such as ‘Astalavista’ and ‘milw0rm,’ as well as the popular image-host ‘ImageShack,’ have given the movement worldwide media attention.
The ‘anti-security movement” as it is understood today was coined a document which was initially an index on the anti.security.is website: ‘The purpose of this movement is to encourage a new policy of anti-disclosure among the computer and network security communities. The goal is not to ultimately discourage the publication of all security-related news and developments, but rather, to stop the disclosure of all unknown or non-public exploits and vulnerabilities. In essence, this would put a stop to the publication of all private materials that could allow script kiddies from compromising systems via unknown methods.’
Grey Hat
A grey hat in the hacking community refers to a skilled hacker whose activities fall somewhere between white hat (lawful) and black hat (unlawful) hackers on a variety of spectra.
They usually do not hack for personal gain or have malicious intentions, but may be prepared to technically commit crimes during the course of their technological exploits in order to achieve better security. Whereas white hat hackers will tend to advise companies of security exploits quietly, grey hat hackers are prone to ‘advise the hacker community as well as the vendors and then watch the fallout.’
read more »
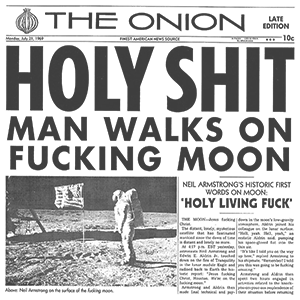
Our Dumb Century
‘Our Dumb Century: The Onion Presents 100 Years of Headlines from America’s Finest News Source’ is a satirical humor book written by the staff of ‘The Onion’ and published in 1999. The chief editor of the book was Scott Dikkers, with specific sections edited by Robert D. Siegel, Maria Schneider, and John Krewson.
The book, spun off from ‘The Onion’ weekly-newspaper format of dryly satirizing current events, features mocked-up newspaper front pages from the entire 20th century, presented as though ‘The Onion’ had been continuously in print since before 1900. The publication of the book is in itself a parody of other end of the century retrospectives that had been published in 1999, notably ‘Time’ magazine and ‘The New York Times.’
read more »
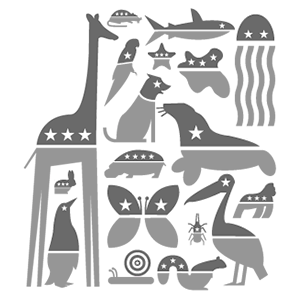
Shark Repellent
‘Poison pill’ is sometimes used more broadly to describe other types of takeover defenses that involve the target taking some action.
Although the broad category of takeover defenses (more commonly known as ‘shark repellents‘) includes the traditional shareholder rights plan poison pill. Other anti-takeover protections include: Limitations on the ability to call special meetings or take action by written consent; Supermajority vote requirements to approve mergers; and Supermajority vote requirements to remove directors.
read more »
Wedge Issue
A wedge issue is a social issue, often of a divisive or controversial nature, which splits apart a population or political group. Wedge issues can be advertised or publicly aired in an attempt to weaken the unity of a population; with the goal of enticing polarized individuals to give support to an opponent. The use of wedge issues gives rise to wedge politics. Wedge issues are also known as ‘hot button’ or ‘third rail’ issues.
Political campaigns use wedge issues to exploit tension within a targeted population. A wedge issue may often be a point of internal dissent within an opposing party, which that party attempts to suppress or ignore discussing because it divides ‘the base.’ Typically, wedge issues have a cultural or populist theme, relating to matters such as crime, national security, sexuality (e.g. gay marriage), or race. A party may introduce a wedge issue to an opposing population, while aligning itself with the dissenting faction of the opposition.
read more »
Poison Pill
A shareholder rights plan, colloquially known as a ‘poison pill,’ is a type of defensive tactic used by a corporation’s board of directors against a takeover. There are a number of such tactics, referred to as ‘shark repellents’ generally. In the field of mergers and acquisitions, shareholder rights plans were devised in the early 1980s as a way for directors to prevent takeover bidders from negotiating a price for sale of shares directly with shareholders, and instead forcing the bidder to negotiate with the board.
Shareholder rights plans are unlawful without shareholder approval in many jurisdictions such as the United Kingdom, frowned upon in others such as throughout the European Union, and lawful if used ‘proportionately’ in others, including Delaware in the United States. They are controversial because they hinder an active market for corporate control. Further, giving directors the power to deter takeovers puts directors in a position to enrich themselves, as they may effectively ask to be compensated for the price of consenting to a takeover.
read more »
Mouseland
The Story of Mouseland was first told first by Canadian politician Clarence Gillis, and later and most famously by Tommy Douglas, leader of the Saskatchewan Co-operative Commonwealth Federation and, later, the New Democratic Party of Canada, both social democratic parties.
It was a political fable expressing the CCF’s view that the Canadian political system was flawed in offering voters a false dilemma: the choice of two parties, neither of which represented their interests. The mice voted in black cats, which represented the Progressive Conservative Party, and then they found out how hard life was. So they voted in the white cats, which symbolized the Liberal Party.
read more »
Duverger’s Law
In political science, Duverger’s law is a principle which asserts that a plurality rule election system (voters vote for one candidate, and the candidate with the most votes wins) tends to favor a two-party system. This is one of two hypotheses proposed by French sociologist and politician Maurice Duverger, the second stating that ‘the double ballot majority system and proportional representation tend to multipartism.’
Duverger observed the effect and recorded it in several papers published in the 1950s and 1960s. In the course of further research, other political scientists began calling the effect a ‘law’ or principle.
read more »