Cyriak Harris is a British freelance animator better known by his first name Cyriak, or by his pseudonym Mutated Monty. He is known for his surreal short web animations. A regular contributor to the British website B3ta since 2004, Cyriak displays a surreal and often disturbing animation style with a distinct British theme. He uses a combination of Adobe Photoshop and After Effects for his animation and visuals along with FL Studio (formerly known as Fruity Lookps) for original music pieces alongside his videos.
Cyriak
Birds of America
‘The Birds of America‘ is the title of a book by naturalist and painter John James Audubon, containing paintings and scientific description of a wide variety of birds of the United States. It was first published as a series of sections between 1827 and 1838 in Edinburgh and London. The work consists of hand-colored, life-size prints made from engraved plates measuring around 39 by 26 inches. In December of 2010 a copy sold at auction for £7.3 million. The original edition is often regarded as the greatest picture book ever produced. 161 subscribers paid $1,000 each for what ended up to be four volumes.
There are only 11 copies held in private collections out of 119 thought to still exist and it is estimated that out of the top ten most expensive books, five of them would be copies of ‘Birds of America.’ In 2007 the book was the subject of an exhibition by the Teylers Museum (the oldest museum in the Netherlands), which owns a copy it ordered from the original subscription, along with the table sold to house and display it. The book’s subsections fit into special drawers around a fly-leaf table; the table formed the centerpiece for gatherings of the Teyler’s gentleman’s society of science. A low-resolution version of ‘Birds of America’ can be viewed on the Audubon website.
DoS Attack
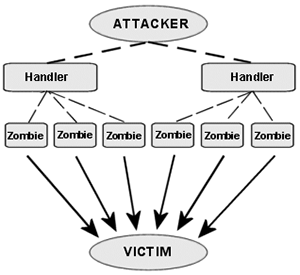
A denial-of-service attack (DoS attack) or distributed denial-of-service attack (DDoS attack) is an attempt to make a computer resource unavailable to its intended users. Perpetrators of DoS attacks typically target sites or services hosted on high-profile web servers such as banks, credit card payment gateways, and even root nameservers. The term is generally used with regards to computer networks, but is not limited to this field, for example, it is also used in reference to CPU resource management. DoS attacks are prosecuted in a number of nations under a variety of computer crime laws. They can also constitute acts of cyberwarfare.
One common method of attack involves saturating the target machine with external communications requests, such that it cannot respond to legitimate traffic, or responds so slowly as to be rendered effectively unavailable. In general terms, DoS attacks are implemented by either forcing the targeted computer(s) to reset, or consuming its resources so that it can no longer provide its intended service or obstructing the communication media between the intended users and the victim so that they can no longer communicate adequately.
Broken Windows Theory
Broken windows theory states that monitoring and maintaining urban environments in a well-ordered condition prevents vandalism as well as an escalation into more serious crime, i.e. failure to replace a broken window invites further vandalism to the building and neighborhood. It is a criminological theory introduced in an 1982 article in the ‘Atlantic Monthly’ by social scientists James Q. Wilson and George L. Kelling, which has received support from several empirical studies, and has also been the subject of a large body of criticism. Former NY mayor, Rudy Giuliani was a proponent of the broken windows theory, and aggressively policed minor offenses like subway fare evasion, public urination, and ‘squeegee men,’ and other panhandlers. Crime dropped precipitously during Giuliani’s tenure, but so did crime nationwide during a period of extended economic growth in the 1990s.
A successful strategy for preventing vandalism, according to the theory, is to fix the problems when they are small. Repair the broken windows within a short time, a day or a week, and the tendency is that vandals are much less likely to break more windows or do further damage. Clean up the sidewalk every day, and the tendency is for litter not to accumulate (or for the rate of littering to be much less). The theory thus makes two major claims: that further petty crime and low-level anti-social behavior will be deterred, and that major crime will, as a result, be prevented. Criticism of the theory has tended to focus only on the latter claim.
Parable of the Broken Window
The parable of the broken window was introduced by French economist and political theorist Frédéric Bastiat in his 1850 essay Ce qu’on voit et ce qu’on ne voit pas (That Which Is Seen and That Which Is Unseen) to illustrate the hidden costs associated with destroying property of others. The parable, also known as the broken window fallacy, demonstrates how the law of unintended consequences affects economic activity people typically see as beneficial.
read more »
Combination Puzzle
A combination puzzle, also known as a sequential move puzzle or twisty puzzle, is a puzzle which consists of a set of pieces which can be manipulated into different combinations by a group of operations. The puzzle is solved by achieving a particular combination starting from a random (scrambled) combination. Often, the solution is required to be some recognizable pattern such as ‘all like colors together’ or ‘all numbers in order’. The most famous of these puzzles is the original Rubik’s Cube, invented in 1974 by Hungarian sculptor and professor of architecture Ernő Rubik.
There are many different variations including cubes with up to seven layers: the 2×2×2 (Pocket/Mini Cube), 3×3×3 cube (Rubik’s Cube), the 4×4×4 (Rubik’s Revenge/Master Cube), and the 5×5×5 (Professor’s Cube), the 6×6×6 (V-Cube 6), and 7×7×7 (V-Cube 7). The E-cube is an electronic variant of the 3x3x3 cube, made with RGB LEDs and switches. In addition to cubes, combination puzzles are available in various other geometric shapes, including a tetrahedron (Pyraminx), octahedron (Skewb Diamond), dodecahedron (Megaminx), and icosahedron (Dogic). There are also puzzles that change shape such as Rubik’s Snake and the Square One.