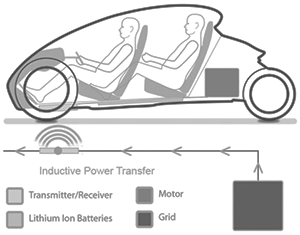
Wireless power or wireless energy transmission is the transmission of electrical energy from a power source to an electrical load without man-made conductors. Wireless transmission is useful in cases where interconnecting wires are inconvenient, hazardous, or impossible. The problem of wireless power transmission differs from that of wireless telecommunications, such as radio. In the latter, the proportion of energy received becomes critical only if it is too low for the signal to be distinguished from the background noise.
With wireless power, efficiency is the more significant parameter. A large part of the energy sent out by the generating plant must arrive at the receiver or receivers to make the system economical. The most common form of wireless power transmission is carried out using direct induction followed by resonant magnetic induction. Other methods under consideration are electromagnetic radiation in the form of microwaves or lasers and electrical conduction through natural media.
read more »
Wireless Power
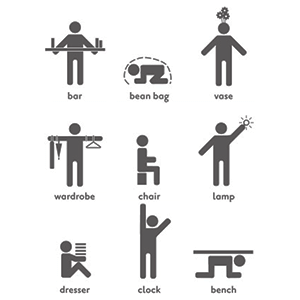
Human Furniture
Human furniture (or forniphilia) is a form of bondage and sexual objectification in which a person’s body is incorporated into a chair, table, cabinet or other piece of furniture. The term was originally coined by bondage aficionado Jeff Gord.
Forniphilia is an extreme form of bondage because the subject usually is tightly bound and expected to stay immobile for a prolonged period. They are often gagged and/or placed in position where there is a danger of being smothered. Proper safety requires frequent checks of the submissive’s well-being.
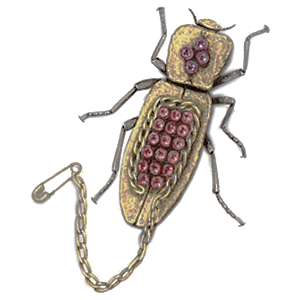
Live Insect Jewelry
Live insect jewelry refers to jewelry, made from living creatures- usually bejeweled, large insects- which is worn as a fashion accessory. The use of insects as live jewelry has existed for many centuries, with the Egyptians believed to have been the first to have worn insects as jewelry. Ancient Egyptian soldiers commonly wore scarab beetles into battle as the beetles were considered to have supernatural powers of protection against enemies.
Although live jewelry has featured in Mayan cultural traditions for many centuries, it was not until the 1980s that the Mexican Maquech Beetle, a sub-species of the Zopherus beetle, achieved mainstream popularity as live jewelry. The Maquech Beetle is a large, docile, wingless insect which is decorated with gold and semi-precious gemstones and is attached to a decorative safety pin by a chain leash.
read more »
Jerky
Jerky is lean meat that has been trimmed of fat, cut into strips, and then dried to prevent spoilage. Normally, this drying includes the addition of salt, to prevent bacteria from developing on the meat before sufficient moisture has been removed. The word ‘jerky’ is a corruption of the Spanish ‘charqui,’ which is from the Quechua word ‘ch’arki,’ which means to burn (meat). All that is needed to produce basic ‘jerky’ is a low-temperature drying method, and salt to inhibit bacterial growth.
Modern manufactured jerky is normally marinated in a seasoned spice rub or liquid, and dried, dehydrated or smoked with low heat. Some makers still use just salt and sun-dry fresh sliced meat to make jerky. Some product manufacturers finely grind meat, mix in seasonings, and press the meat-paste into flat shapes prior to drying. Jerky is ready-to-eat and needs no additional preparation. It can be stored for months without refrigeration. When the protein to moisture content ratio is correct, the resulting meat is cured, or preserved.
read more »
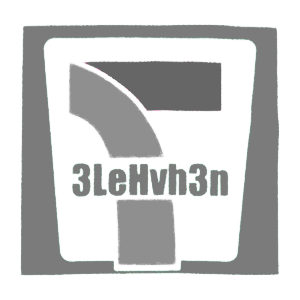
Jejemon
Jejemon is a pop culture phenomenon in the Philippines. According to ‘Urban Dictionary,’ a Jejemon is a person ‘who has managed to subvert the English language to the point of incomprehensibility.’ ‘The Philippine Daily Inquirer’ describes Jejemons as a ‘new breed of hipster who have developed not only their own language and written text but also their own subculture and fashion.’ Short-hand typing was first popularized by text messaging (limited to 160 characters per text). As a result, an ‘SMS language’ developed in which words were shortened in order to fit the 160-character limit.
The Jejemons are said to be the new jologs, a term used for Filipinos of the lower income class. The sociolect of the Jejemons, called Jejenese, is derived from English, Filipino and their code-switched variant, Taglish. It has its own, albeit unofficial, orthography, known as Jejebet, which uses the Filipino variant of the Roman alphabet, Arabic numerals and other special characters. Words are created by rearranging letters in a word, alternating capitalization, with an over-usage of the letters H, X or Z, and silent letters. It has similarities with Leetspeak, primarily the alphanumeric nature of its writing.
Jediism
Jediism is a religion based on the philosophical and spiritual ideas of the Jedi as depicted in the science fiction film ‘Star Wars.’ It has no founder or central structure, but was the most selected ‘alternative faith’ in a census of England and Wales. Jediism became accepted as a religion following the Jedi census phenomenon in 2001 and the preceding email campaign to put ‘Jedi’ in answer to the census religion classification question.
The phenomenon attracted the attention of sociologist of religion Adam Possamai who analyzed it in the framework of what he dubs ‘hyper-real religion’ (religions inspired by popular culture). Jediism believers align themselves with the moral code demonstrated by the fictional Jedi. According to the Temple of the Jedi Order website, Jediism is a syncretistic religion, incorporating beliefs from various religious philosophies including Christianity, Sufism (Islam), Stoicism, Buddhism, Taoism, and Shintoism.
read more »
Phishing
Phishing is the act of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors, or IT administrators are commonly used to lure the unsuspecting public. Phishing emails may contain links to websites that are infected with malware.
Phishing is typically carried out by e-mail spoofing (altering the sender address) or instant messaging, and it often directs users to enter details at a fake website whose look and feel are almost identical to the legitimate one. Phishing is an example of social engineering (manipulating people into performing actions or divulging confidential information), and exploits the poor usability of current web security technologies. Attempts to deal with the growing number of reported phishing incidents include legislation, user training, public awareness, and technical security measures.
read more »
Comment Crew
PLA Unit 61398, referred to by the US as the ‘Comment Crew’ (owing to the collective’s past pattern of embedding HTML commands in the comments section of popular websites) is an alleged cyber-warfare unit of the Chinese military. As a hacker group the entity has been known to US intelligence agencies since 2002; they gave it the codename ‘Byzantine Candor.’
The unit is reported to operate out of a 12-story building in Shanghai and the surrounding neighborhood. The story was first broken by the ‘New York Times,’ based on information from a report by the computer security firm Mandiant, who were retained by the New York Times after a compromise of their own computer systems. Mandiant’s report states that PLA Unit 61398 is believed to be under the 2nd Bureau of the People’s Liberation Army General Staff’s Department (GSD) 3rd Department and that there is evidence that it contains an entity Mandiant calls APT1, part of the Advanced Persistent Threat attacking American corporations and government entities.
Chaos Computer Club
The Chaos Computer Club (CCC) is one of the world’s biggest hackers organizations. The CCC is based in Germany and other German-speaking countries. The CCC describes itself as ‘a galactic community of life forms, independent of age, sex, race or societal orientation, which strives across borders for freedom of information….’ In general, the CCC advocates more transparency in government, freedom of information, and the human right to communication.
Supporting the principles of the hacker ethic, the club also fights for free universal access to computers and technological infrastructure. The CCC was founded in Berlin in 1981 at a table which had previously belonged to the Kommune 1 (the first politically motivated commune in Germany) in the rooms of the newspaper ‘Die Tageszeitung’ by Wau Holland and others in anticipation of the prominent role that information technology would play in the way people live and communicate.
read more »
2600: The Hacker Quarterly
2600: The Hacker Quarterly is an American publication that specializes in publishing technical information on a variety of subjects including telephone switching systems, Internet protocols and services, as well as general news concerning the computer ‘underground’ and left wing, and sometimes (but not recently), anarchist issues.
The magazine’s name comes from the phreaker discovery in the 1960s that the transmission of a 2600 hertz tone (which could be produced perfectly with a plastic toy whistle given away free with Cap’n Crunch cereal—discovered by friends of John Draper) over a long-distance trunk connection gained access to ‘operator mode’ and allowed the user to explore aspects of the telephone system that were not otherwise accessible.
read more »